Web Development and eCommerce Specialists
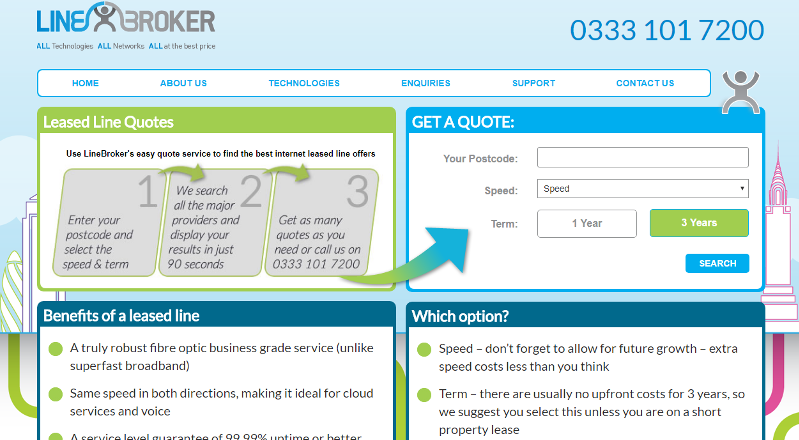
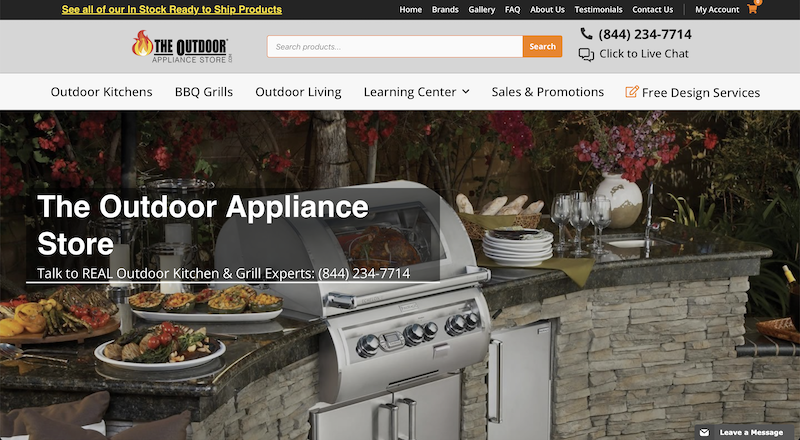
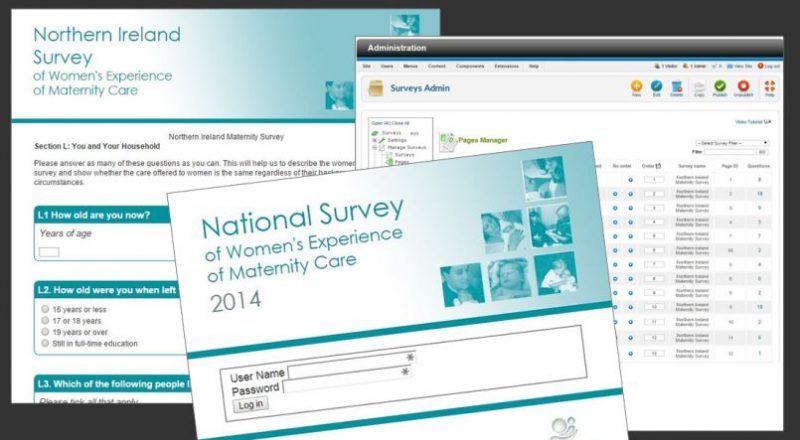
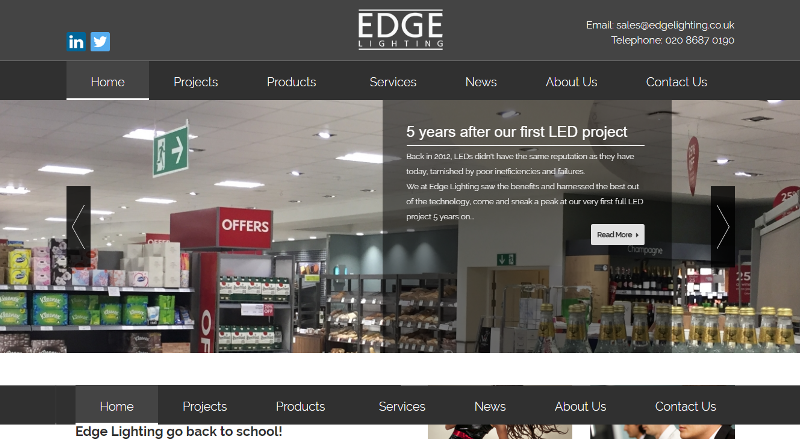
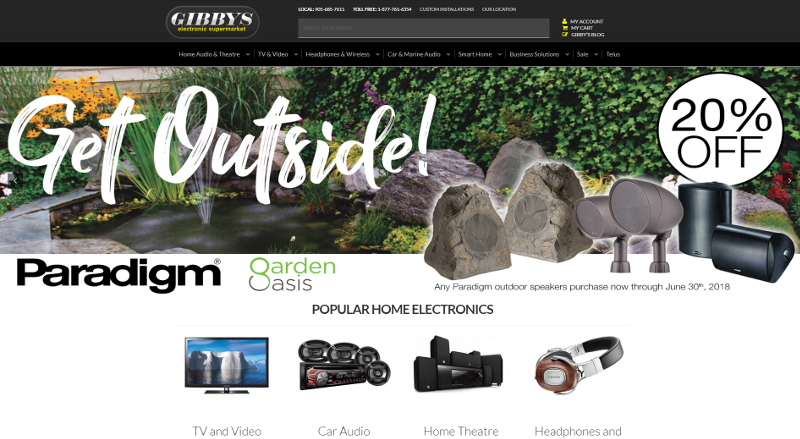
Paramount is a Web Development and eCommerce Specialist working with clients retailing online.
With a strong background in eCommerce and Web Development stretching back to 2005; Paramount uses industry standard WordPress with WooCommerce and Shopify as fully scalable eCommerce engines. Paramount works on building, maintaining and developing the underlying infrastructure to help clients retail successfully online.
Paramount’s clients are established businesses looking for an experienced eCommerce partner to assist in the maintenance, support, development and growth of their eCommerce presence.
If you are:
• running an eCommerce platform that is not the right fit for your business
• looking for a replacement eCommerce platform
• in need of an eCommerce partner to assist you in managing your eCommerce platform
then Paramount is the perfect fit for you.